Maximizing Service Defense: The Ultimate Overview to Electronic Security Solutions
In the hectic and ever-evolving landscape of service safety, the reliance on electronic protection options has come to be paramount for protecting useful properties, confidential information, and preserving functional connection. In this overview to electronic protection options, we will discover the most recent fads, advanced modern technologies, and finest practices to strengthen your business versus potential threats and vulnerabilities.
Relevance of Electronic Safety Solutions
When thinking about the security of properties and sensitive details, the importance of digital security services can not be overstated. In today's interconnected globe, where cyber dangers are constantly progressing and becoming much more advanced, businesses should focus on implementing robust digital security procedures to safeguard their data and procedures. Digital safety solutions encompass a vast array of technologies and techniques designed to safeguard versus unapproved accessibility, information violations, malware, and various other cyber hazards.
Among the crucial advantages of electronic safety and security options is their ability to supply real-time surveillance and hazard detection. BQT Locks. With tools like breach detection systems, firewalls, and security information and event management (SIEM) systems, organizations can proactively determine and react to safety cases before they intensify right into significant breaches. In addition, electronic safety and security options assist make certain compliance with sector laws and criteria, shielding organizations from possible legal and economic consequences
Sorts Of Electronic Protection Systems
Provided the vital importance of electronic security services in protecting companies against cyber risks, it is necessary to discover the numerous kinds of digital protection systems readily available to boost security and durability. One of the most typical types of electronic security systems is the firewall, which acts as an obstacle in between a business's internal network and exterior networks, filtering out possibly damaging information. By employing a mix of these digital safety systems, services can develop a durable defense against numerous protection hazards.
Carrying Out Accessibility Control Steps
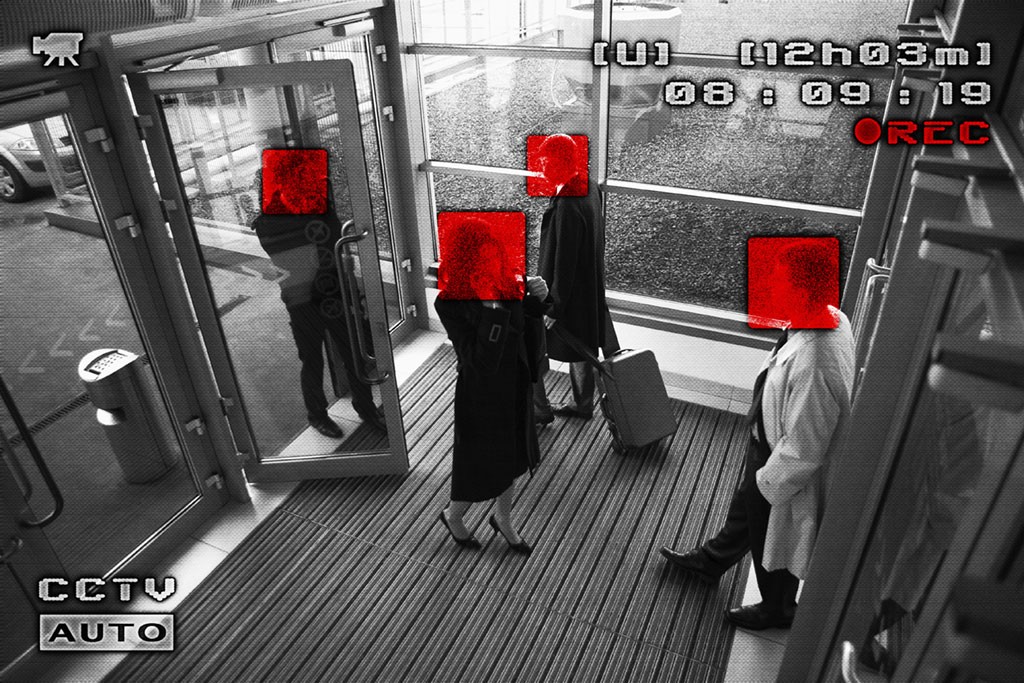
In addition, gain access to control measures can be integrated with monitoring systems to check and record individuals' motions within safeguarded areas. This assimilation boosts security by offering a thorough overview of who is accessing specific places at any type of offered time. Moreover, access control systems can be set up to restrict accessibility based on time, location, or individual credentials, allowing companies to personalize safety methods according to their particular needs.
Cybersecurity Ideal Practices
To improve overall safety position, applying robust cybersecurity ideal techniques is essential in securing digital properties and data honesty. Conducting regular safety audits and evaluations aids recognize weak points and locations for renovation.
Developing a thorough incident action strategy enables swift and efficient feedbacks to safety and security breaches, lessening potential damage. Securing delicate information both en route and at rest provides an additional barrier versus information breaches. Applying access controls based on the principle of least benefit restricts the direct exposure of vital systems and details to only find out this here those who require it for their roles. Normal backups of information ensure that in the event of a ransomware assault or information loss, important information can be recuperated. Embracing a positive strategy to cybersecurity via constant tracking and danger knowledge aids detect and mitigate potential dangers before they intensify. By including these ideal techniques right into cybersecurity strategies, companies can fortify their defenses versus advancing cyber threats.
Security and Monitoring Solutions

Video surveillance options offer remote tracking capabilities, enabling accredited personnel to watch on the properties even when off-site. Furthermore, advanced attributes like motion discovery, face recognition, and permit plate acknowledgment enhance the general protection position of the company. Incorporating security systems with security system and gain access to control additionally reinforces the safety infrastructure, making it possible for a positive reaction to prospective protection violations.
Final Thought
In conclusion, digital protection options are necessary for maximizing BQT Locks business defense. It is crucial to invest in the appropriate digital official source safety and security systems to make certain the safety and security and safety and security of the company.